.png)
The "FREE" Tools List


Packet Sender can send and receive UDP, TCP, and SSL on the ports of your choosing. It also has a built-in HTTP client for GET/POST requests and Panel Generation for the creation of complex control systems.
Aircrack-ng


Aircrack-ng is a complete suite of tools to assess WiFi network security.
It focuses on different areas of WiFi security:
Monitoring: Packet capture and export of data to text files for further processing by third party tools Attacking: Replay attacks, deauthentication, fake access points and others via packet injection Testing: Checking WiFi cards and driver capabilities (capture and injection) Cracking: WEP and WPA PSK (WPA 1 and 2)
iPerf3
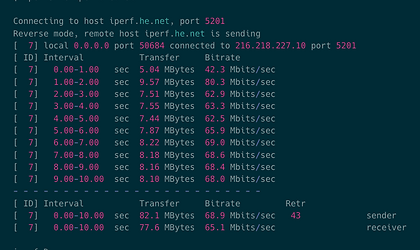

iPerf3 is a tool for active measurements of the maximum achievable bandwidth on IP networks. It supports tuning of various parameters related to timing, buffers and protocols (TCP, UDP, SCTP with IPv4 and IPv6). For each test it reports the bandwidth, loss, and other parameters.
List of iperf related articles
https://www.networkdatapedia.com/technology-articles/search/iperf
Maresware


Maresware was originally designed to assist law enforcement personnel in the analysis and processing of computer related evidence.
Maresware was designed to handle extremely large amounts of data and to do so at maximum speed. Therefore, it was written in pure "C", which outperforms most other languages. Today, it can process those large amounts of giga and tera bytes of data fast and efficiently.
Nagios XI


Nagios monitors the network for problems caused by overloaded data links or network connections, as well as monitoring routers, switches and more.
Easily able to monitor availability, uptime and response time of every node on the network, Nagios can deliver the results in a variety of visual representations and reports.
Nmap – Plus


Nmap is one of the most comprehensive sites that is run by Gordon Lyon, (Fyodor) that covers so many different tools and technologies it is best to just go to his site – download, play and learn.
Fyodor is a well-known Technologist, writer and teacher. He is one of the GOOD hackers that uses his skills to teach and help network people learn about their world in so many ways.
List of related articles
https://www.networkdatapedia.com/technology-articles/search/nmap
NetworkMiner


NetworkMiner can be used as a passive network sniffer/packet capturing tool in order to detect operating systems, sessions, hostnames, open ports etc. without putting any traffic on the network.
NetworkMiner makes it easy to perform advanced Network Traffic Analysis (NTA) by providing extracted artifacts in an intuitive user interface. The way data is presented not only makes the analysis simpler, it also saves valuable time for the analyst.
Sensu


Sensu is the open source monitoring event pipeline built to reduce operator burden and make developers and business owners happy.
Started in 2011, Sensu’s flexible approach solves the challenges of monitoring hybrid-cloud and ephemeral infrastructures with scalable, automated workflows and integrations with tools you already use.
Get started now and feel the #monitoringlove
TraceWrangler


TraceWrangler is a network capture file toolkit running on Windows (or on Linux, using WINE) that supports PCAP as well as the new PCAPng file format, which is now the standard file format used by Wireshark.
The most prominent use case for TraceWrangler is the easy sanitization and anonymization of PCAP and PCAPng files
Related articles
https://www.networkdatapedia.com/technology-articles/search/tracewrangler
Vistumber


Uses the Windows Native Wifi API or netsh to find access points and get wireless information GPS Support.
Export/Import access points from Vistumbler TXT/VS1/VSZ or Netstumbler TXT NS1 Export access point GPS locations to a google earth kml file or GPX (GPS eXchange format) Live Google Earth Tracking - Auto KML automatically shows access points in google earth.
Wireshark


Wireshark is the world’s foremost and widely-used network protocol analyzer.
It lets you see what’s happening on your network at a microscopic level and is the de facto (and often de jure) standard across many commercial and non-profit enterprises, government agencies, and educational institutions.
List of related articles
https://www.networkdatapedia.com/technology-articles/search/wireshark
hrping

hrPing - High-precision ping utility
-
Graphical display of ping results
-
Uses high resolution timers, so ping times are accurate to the usec
-
Can ping as well with UDP packets or ICMP timestamp messages
-
Times and handles ICMP error replies as well
-
Can have multiple pings "in-flight", no need to wait for a reply before sending the next ping
-
Improved statistics
-
Size sweep: Send increasing packet sizes
-
Can show only a summary of results